What is a Bayesian Belief Network?
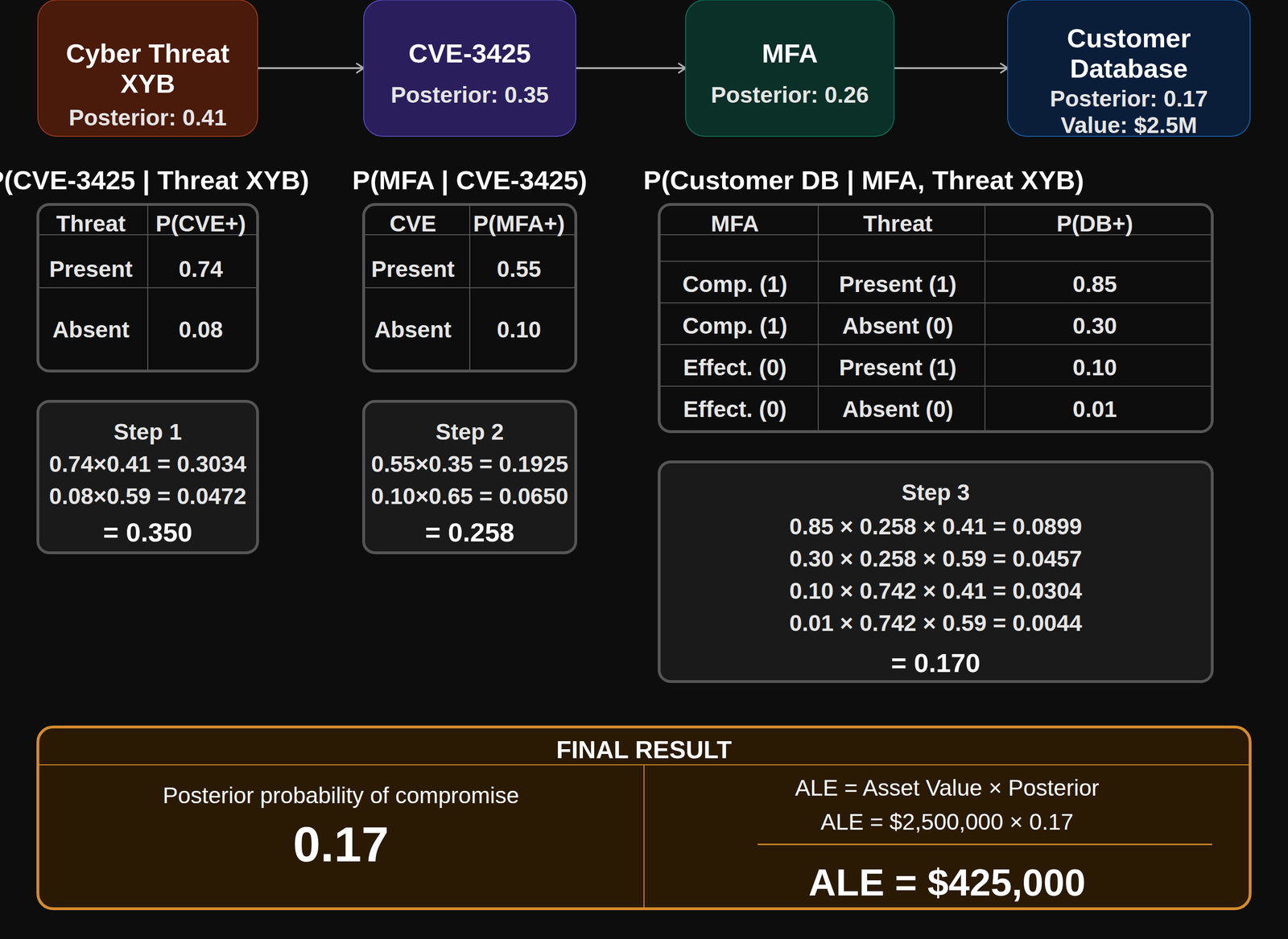
A BBN is a probabilistic graphical model that encodes the conditional relationships between nodes — threat actor, vulnerability, control, and asset. Each node carries a probability that updates based on the state of its parent nodes, propagating belief from threat all the way to financial impact with mathematical rigor. The result is a posterior probability, not a score.
How are the CPT values determined?
Conditional Probability Tables are populated from four traceable sources: public threat intel (CVE severity, CVSS, EPSS); control effectiveness research from NIST and CIS Controls; loss databases including Verizon DBIR and IBM Cost of a Data Breach; and structured expert elicitation for novel threat chains. Over time, observed client outcomes calibrate values further — building a proprietary data asset that compounds in accuracy.
Why is this better than a risk matrix?
Risk matrices assign color-coded severity buckets based on subjective likelihood and impact ratings. They do not propagate conditional dependencies — a change in one node does not automatically update downstream nodes. Ontologic™ models risk as non-linear and interconnected, as it actually behaves. The output is a posterior probability and a dollar figure, not a red/yellow/green cell that a board can ignore.
What is the ALE and why does it matter?
ALE = Asset Value × Posterior Probability of Compromise. This produces the expected annual financial exposure attributable to a specific threat chain — directly comparable to insurance premiums and capital reserve requirements. It is the number a CFO can budget against, a board can hold management accountable for, and an insurer can underwrite against, in a way that CVSS scores and heat maps never could.
Does this expose your IP?
No. What you see here is methodology — Bayesian Belief Networks, conditional probability tables, and ALE calculations are well-established public techniques. What is proprietary is the ontology Ontologic™ has built inside those techniques: how threats, vulnerabilities, controls, and assets are classified, related, and weighted at scale; the calibration methodology; and the CPT libraries accumulated across industries and asset classes.
Who are the four audiences?
CISOs receive technical risk chain detail and control effectiveness scores. CFOs receive ALE figures tied to business assets and revenue impact. Boards receive portfolio-level exposure summaries in plain language. Insurers receive structured risk data that maps directly to underwriting criteria and coverage gap analysis. One Ontologic™ engine. Four translations. Automatically, in real time.